Configure Webhooks
Set up webhooks from your API key’s Webhooks page in the .Set Your Endpoint URL
Enable the webhook toggle and enter your HTTPS endpoint URL. Para will send POST requests to this URL when subscribed events occur.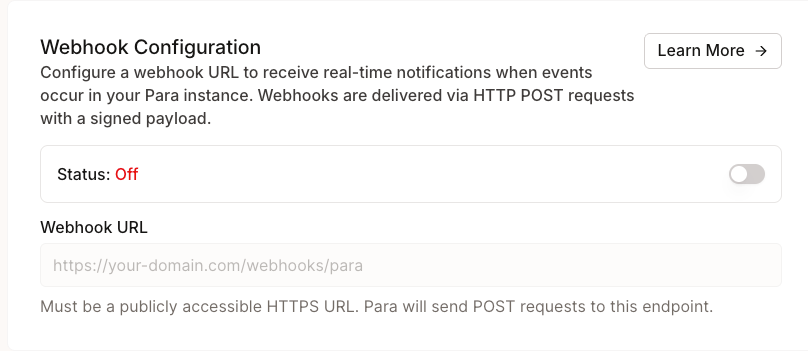
Select Events
Choose which events you want to receive. You must select at least one event type when webhooks are enabled.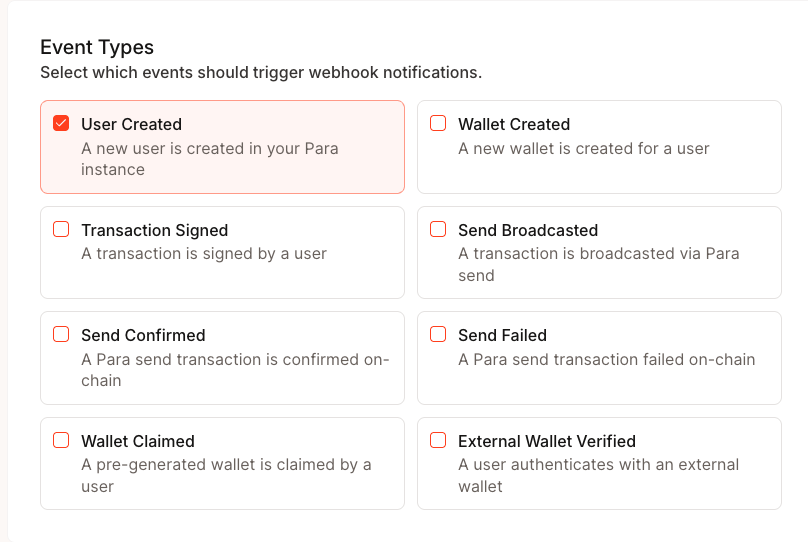
Save and Copy Your Secret
When you first save your webhook configuration, Para generates a signing secret (prefixed withwhsec_). This secret is
displayed only once — copy and store it securely. You’ll use it to
verify webhook signatures.
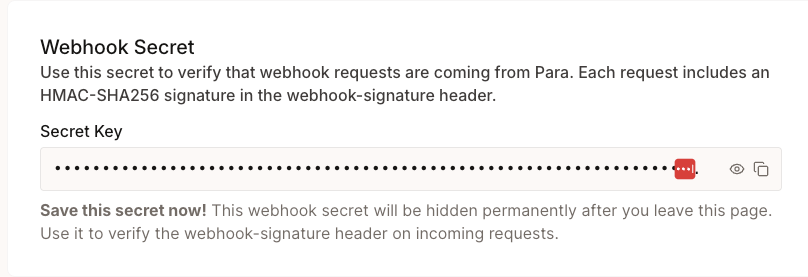
Your webhook secret is shown only at creation and after rotation. If you lose it, you’ll need to rotate to get a new
one.
Test Your Endpoint
Click Test Webhook to send atest.ping event to your endpoint. This verifies connectivity without triggering a
real event.
Event Types
| Event | Description |
|---|---|
user.created | A new user was created |
wallet.created | A new wallet was created for a user |
transaction.signed | A transaction was signed |
send.broadcasted | A Para Send transaction was broadcasted to the network |
send.confirmed | A Para Send transaction was confirmed on-chain |
send.failed | A Para Send transaction failed |
wallet.pregen_claimed | A pre-generated wallet was claimed by a user |
user.external_wallet_verified | A user verified an external wallet |
Event Payload
Every webhook request contains a JSON body with a standard envelope wrapping the event-specific data:| Field | Description |
|---|---|
id | Unique event ID prefixed with evt_ |
type | The event type string |
createdAt | ISO 8601 timestamp of when the event was created |
data | Event-specific payload (see below) |
Event Data by Type
user.created
user.created
wallet.created
wallet.created
transaction.signed
transaction.signed
chainId field is null for message signing operations where no chain is involved.send.broadcasted
send.broadcasted
type will be "SOLANA" and evmChainId will be absent. isDevnet indicates if the transaction was on a devnet.send.confirmed
send.confirmed
send.failed
send.failed
error field is optional and may be absent if no error message was available.wallet.pregen_claimed
wallet.pregen_claimed
user.external_wallet_verified
user.external_wallet_verified
walletProvider field is optional and may be absent depending on how the wallet was connected.Verify Webhook Signatures
Every webhook request includes headers that let you verify the request came from Para:| Header | Description |
|---|---|
webhook-id | Unique event ID (matches payload id) |
webhook-timestamp | Unix timestamp in seconds when the request was sent |
webhook-signature | HMAC-SHA256 signature prefixed with v1, |
- Construct the signed message:
{webhook-timestamp}.{raw request body} - Compute
HMAC-SHA256using your webhook secret as the key - Base64-encode the result and compare it to the signature after the
v1,prefix
Manage Your Webhook
Rotate Secret
If your secret is compromised or you need a new one, rotate it from the Danger Zone section of the Webhooks page. The previous secret remains valid for 24 hours to give you time to update your server. A new secret is displayed once.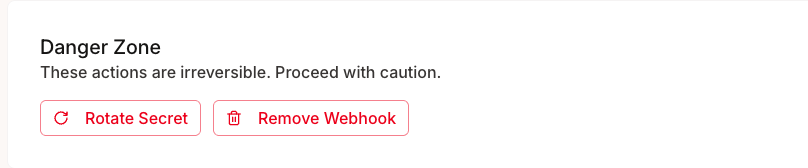
Disable or Delete
Toggle webhooks off to temporarily stop delivery without losing your configuration. To remove the webhook entirely, use the Delete Webhook button — this removes the URL, events, and secret permanently.Best Practices
- Respond quickly: Return a
2xxstatus within a few seconds. Offload heavy processing to a background job. - Verify signatures: Always validate the
webhook-signatureheader before trusting the payload. - Check timestamps: Reject webhooks with timestamps more than 5 minutes old to prevent replay attacks.
- Handle duplicates: Use the
webhook-idheader to deduplicate events in case of retries. - Use HTTPS: Your endpoint must be HTTPS. Para rejects HTTP URLs.